IT & Cybersecurity Student
Independent Security Researcher specialising in web application security, network analysis, and ethical hacking. Passionate about identifying vulnerabilities and building secure systems.
About Me
Cybersecurity student with a passion for finding website vulnerabilities and strengthening digital security by providing mitigations. My journey began at a young age, from studying all night and trying to break into the industry, all the way to formulating a responsible disclosure that protects users.
With experience in security research, OSINT investigations, and network analysis, I bring a practical understanding of modern threats and mitigation strategies, with an ability to translate technical concepts into non-technical terms, ensuring they are distilled into actionable insights.
Having prior access to commercial digital forensics tools and the ability to perform OSINT techniques by experts, I can collect, analyse, and interpret information and/or data publicly available to support investigations, whilst having awareness of digital footprints and the importance of online privacy.
Currently focused on advancing my skills in Web Application Security, Networking, Machine Learning, and AI through independent research and academic projects.
Experience
Technical Lead
- Led a student team in a national cybersecurity competition with real-world scenarios
- Gained exposure to the Security Operations Centre room to understand operations performed
- Performed digital forensic investigations using specialised tools such as XAMN & XRY
- Completed OSINT challenges to solve complex investigative tasks
Independent Security Researcher
- Conducted authorised independent penetration testing and successfully disclosed a reflected XSS vulnerability
- Developed a solution to mitigate the website vulnerability
- Created proof-of-concept payloads demonstrating phishing simulation and data exfiltration risks
- Authored a detailed responsible disclosure report with complete reproduction steps
Project Manager
- Attended a 3-day residential cybersecurity, electrical, and engineering course
- Managed team projects from concept to final brand implementation
- Collaborated to overcome technical challenges in cybersecurity scenarios
- Networked with industry professionals to gain real-world insights
Team Leader
- Led a team of 5 students in pitching a business idea to be implemented if won
- Coordinated instructions and gave roles to each member of the team
- Upon final examination, our team placed 4th nationally across the UK
- Enhanced team collaboration through effective communication strategies
Skills & Security
Hands-on experience across cybersecurity disciplines, backed by real projects, responsible disclosures, and a self-built home lab.
Web App Security
- Reflected XSS discovery & disclosure
- PoC payload development
- Burp Suite · OWASP methodology
Disclosed a real reflected XSS vulnerability via authorised penetration testing. Built PoC payloads, authored a full responsible disclosure report, and developed mitigations.
Proof-of-Concept Development · Burp Suite · Vulnerability Analysis · Responsible Disclosure · XSS Payloads · DOM Manipulation
OSINT & Forensics
- XAMN & XRY forensic tools
- Dark web investigations
- Maltego · Google Dorking · WHOIS
Performed OSINT investigations at CyberFirst Wales using professional tools. Conducted digital forensic analysis with XAMN & XRY used by law enforcement.
Reverse Image Search · Reconnaissance Techniques · Digital Forensics Experience · Dark Web Investigations · Information Gathering · WHOIS Lookup · Google Dorking · Investigation Techniques
Network Security
- Bettercap ARP spoofing & MiTM
- Pi-hole + Unbound DNS
- Tailscale · WireGuard · SSH
Performed live traffic analysis using Bettercap on a controlled network. Configured Pi-hole with Unbound for recursive DNS, and manages VPN tunnels via Tailscale.
Bettercap · Traffic Analysis · TCP/IP · ARP Fundamentals & Spoofing · DNS/DHCP · SSH · VPN Configuration · Firewall Basics
Cryptography
- RSA & quantum vulnerability research
- MD5 hash weaknesses
- CyberChef encryption analysis
Research-level understanding of cryptographic concepts. Studied RSA quantum vulnerabilities, MD5 rainbow table weaknesses, and explored encryption techniques via CyberChef.
Hashing · CyberChef · RSA Concepts · Symmetric Encryption · MD5 Analysis · Rainbow Table Awareness
Threat Analysis
- T-Pot honeypot deployment
- Attack telemetry analysis
- Simulated honeypot experimentation
Deployed T-Pot honeypot on Proxmox to capture simulated attack telemetry. Manipulated attacker behaviour across multiple VMs to gain insight.
T-Pot · Honeypot Configuration · Threat Intelligence · Attack Pattern Analysis · Telemetry Review · Dark Web Data Breaches
Infrastructure
- Proxmox VE administration
- LXC · Docker · VM management
- Headless SSH-only server
Self-built Proxmox homelab running LXC containers, VMs, and self-hosted services. Manages headless server via SSH, configures networking, storage, and backups.
Service Deployment · Headless Server Management · Virtual Machines · Port Configuration · Network Configuration · Backup & Recovery · Monitoring & Logging · Access Control · Linux Fundamentals · Bash · SSH
Programming & Scripting
Python · Bash · C# · HTML/CSS · Node.js · JSON · SQL · API Integration · Hashing · Webhooks · Linux Fundamentals · Visual Studio · VSCode
Soft Skills
Technical Communication · Confidentiality · Project Management · Accountability · Analytical Thinking · Problem Solving · Attention to Detail · Time Management · Adaptability · Collaboration · Leadership · Critical Thinking · Creativity & Innovation
Featured Projects
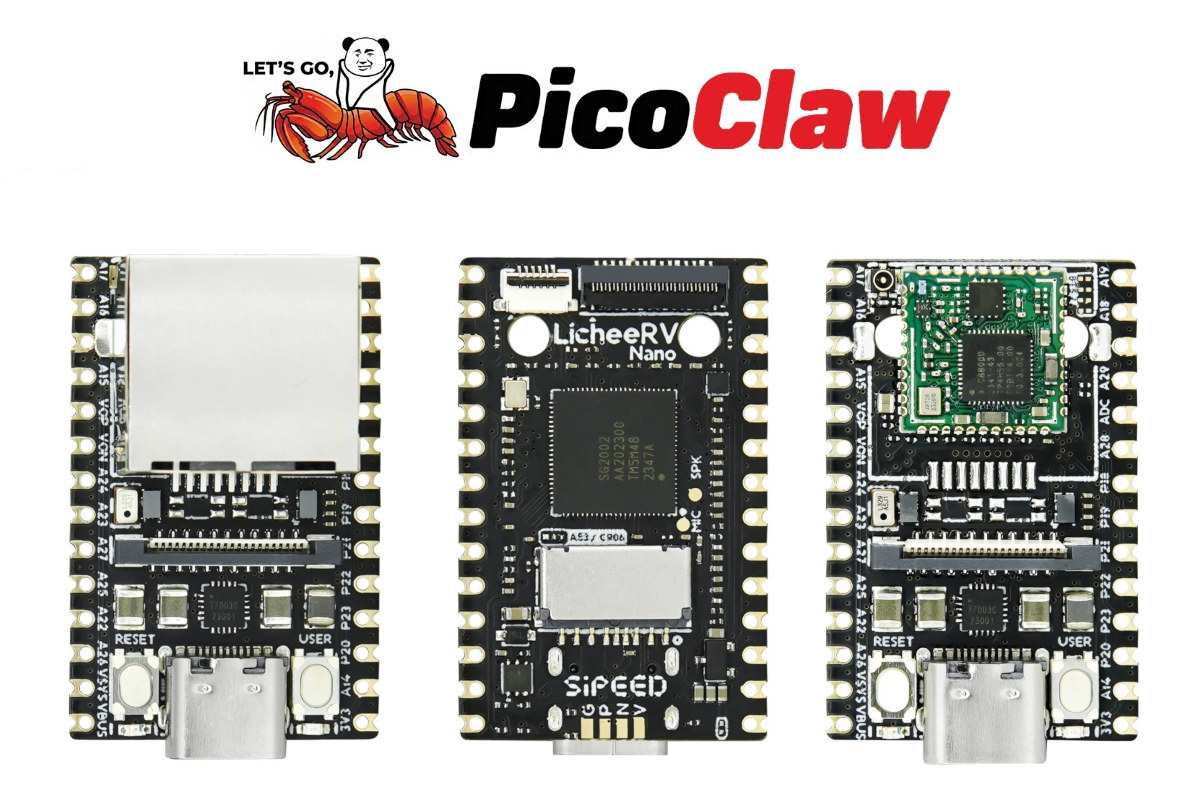
PicoClaw
Integrated an autonomous agent framework using the dedicated Docker image and external LLM APIs to automate tasks and scheduling.
- Containerised an AI agent with Docker for clean, reproducible execution
- Integrated external LLM APIs with webhooks for event-driven task automation
- Scheduled fully autonomous runs using cron-based orchestration
Network Monitoring Analysis
Performed traffic analysis using Bettercap to enhance my understanding of the importance of HTTPS, HTTP vulnerabilities & Wi-Fi security.
- Executed ARP spoofing to position as MiTM and intercept live traffic
- Captured unencrypted HTTP credentials using Bettercap packet sniffing
- Demonstrated how easily unsecured network traffic can be read

Triple-Boot System Configuration
Configured a multi-boot environment with Windows and two Linux distributions for experimentation, self-learning, and feasibility.
- Designed a partition layout supporting three Operating Systems on a single drive
- Configured GRUB bootloader to allow seamless switching
- Planned OS installation sequence and disabled secure boot to avoid bootloader conflicts
Web Security Research
Conducted comprehensive vulnerability assessment on a website application, identifying and responsibly disclosing a security flaw, creating proof-of-concept payloads and providing mitigations.
- Identified a reflected XSS vulnerability through manual payload testing
- Crafted proof-of-concept payloads demonstrating session hijacking potential
- Simulated a phishing scenario to illustrate real-world exploit impact
Simulated Honeypot
Experimented with a high-interaction simulated honeypot framework made by Evilputer to gain an understanding of the behaviour on the backend.
- Probed deceptive services to understand attacker enumeration behaviour
- Examined bogus credentials being used in Telnet-style attack surfaces to increase realism
- Observed how a high-interaction honeypot mimics a real compromised host
- Implied potential to oversee lateral movement techniques within the honeypot environment
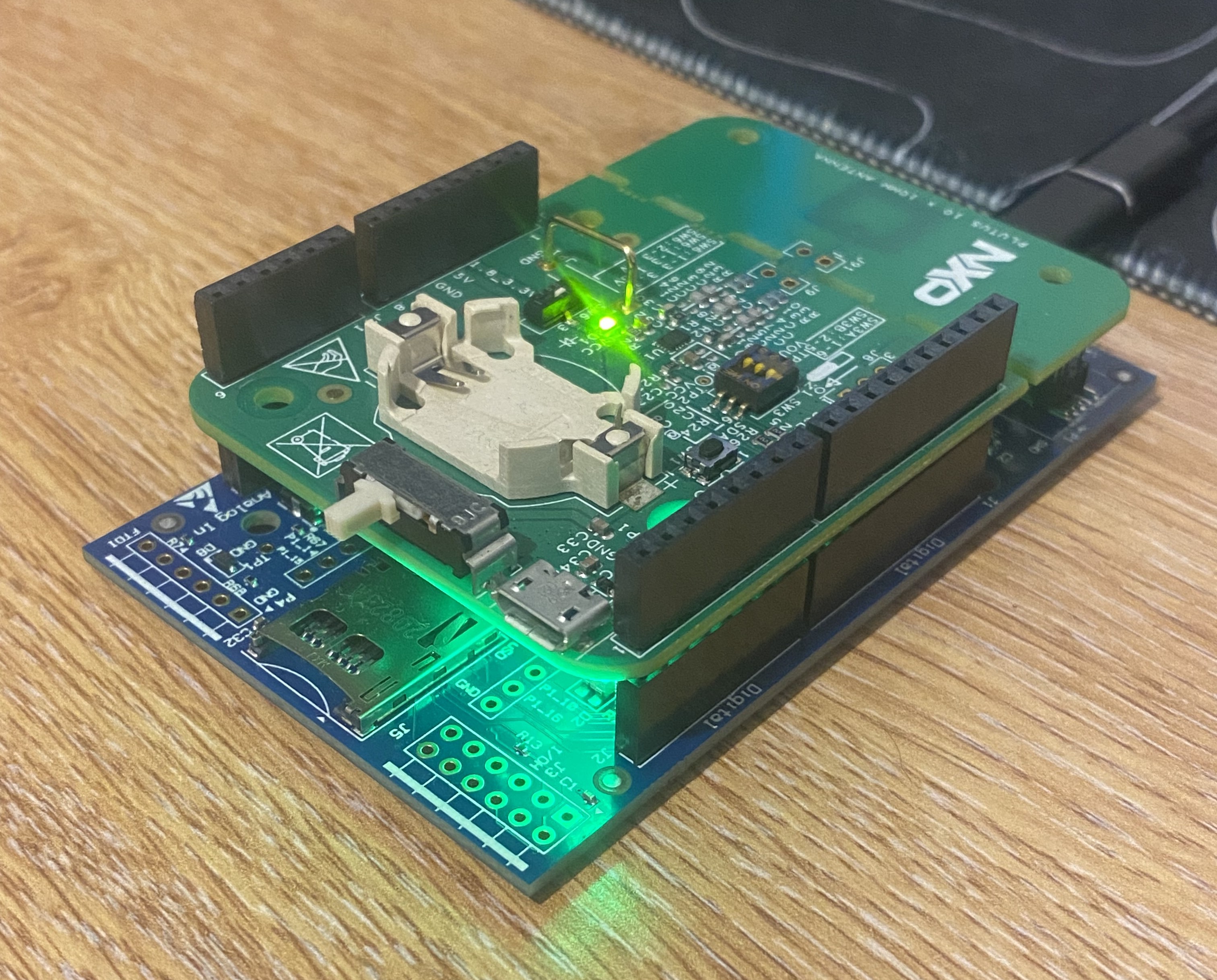
NXP's NFC Authentication Pipeline Investigation
Set up bare-metal firmware on an NXP internal evaluation board to communicate with an SLRC610 NFC reader via LPCOpen, and debugged a hardware-level failure traced to missing components.
- Configured bare-metal firmware using MCUXpress & LPCOpen on the LPC11U37H
- Diagnosed a hardware communication failure traced to missing components on the NFC board via live debugger inspection
- Queried datasheet analysis via the official NXP library to gain understanding of the protocol stack
NeuralRevise
Built an autonomous web agent using Playwright and a local LLM to navigate and complete MCQ-based revision tasks, with an adaptive memory system that learns from correct outcomes over time.
- Investigated Cloudflare bot detection mechanisms and bypassed them by attaching to a real Chrome session via Chrome DevTools Protocol
- Benchmarked llama3.1:8b accuracy across A-Level CS topic areas, identifying weak spots in methodology questions
- Studied adaptive memory as a replacement for repeated LLM inference, achieving 95%+ accuracy after a full question bank run

ChatLlama
Created a self-hosted WhatsApp bot on a Debian 12 LXC that routes messages to a local Ollama instance, enabling private AI conversations on your behalf.
- Provisioned two Debian 12 LXCs on Proxmox with one for the gateway, and one for Ollama with inter-LXC communication
- Integrated whatsapp-web.js with Puppeteer running headless Chrome in a root LXC environment
- Configured sliding window context memory retaining the last 10 messages per session
Home Lab Infrastructure
I run a self-built Proxmox home lab on an Intel i7-7700 with 32GB RAM and roughly ~1TB of storage, designed for hands-on cybersecurity research, network analysis, and breaking systems along the way, but safely.
My environment hosts isolated VMs, LXC containers, and dedicated services for various use cases, such as log analysis, secure remote access, and local AI experimentation. Every component I deploy is isolated and monitored by me rather than relying on third-party platforms.
Education
Childwall Sports & Science Academy
- BTEC IT
- GCSE Computer Science
- GCSE Business Studies
- GCSE Triple Science
The Studio School
- A-level Computer Science
- AAQ Computing
- A-level Business Studies
University of Liverpool Scholar
- Competitive access programme for high-achieving students
- University-level mentoring & academic workshops
- On-site campus experience at UoL
Revision Resources
Free, spec-aligned notes and flashcard apps for AAQ Computing and A-Level CS OCR.Beta
Information may be incorrect. Please verify against the official specifications and use at your own discretion. I am not responsible for any inaccuracies or issues that may arise from using these resources.
Get In Touch
Available for security research collaborations, internships, and cybersecurity opportunities.